CNC Machine Security Risks Part 3
Cyber Threats
This a few-element website sequence explores the risks connected with CNC equipment
Study time: ( phrases)
In this final set up of our a few-element blog site series, we lay out countermeasures that enterprises can do to shield their devices. We’ll also discuss our dependable disclosure as nicely as the opinions we acquired from the sellers we evaluated.
Countermeasures
We located that only two of the 4 vendors analyzed help authentication. Neither of them has authentication enabled by default, which leaves the equipment susceptible to attacks by malicious end users. Enabling authentication is important for shielding Industry 4. attributes from abuse.
Resource accessibility handle techniques are essential for reducing the influence of attacks. Lots of systems allow entry to all a controller’s sources, which can be hazardous. A right approach is to adopt resource obtain regulate methods that grant confined entry. This will aid to guarantee that only licensed customers have access to the controller’s assets and that these means are secured from unauthorized obtain.
When it will come to integrators and close end users, we advise these countermeasures:
- Context-aware industrial intrusion prevention and detection programs (IPS/IDSs): These equipment, which have not too long ago seen a surge in reputation in the catalogues of stability distributors, are outfitted with network engines that can capture authentic-time website traffic connected with industrial protocols to detect attacks.
- Network segmentation: Suitable network architecting is of fantastic relevance. As our research has exposed, all the examined equipment expose interfaces that could be abused by miscreants.
- Appropriate patching: Contemporary CNC equipment are equipped with comprehensive-fledged operating units and intricate software package, which may well inevitably contain protection vulnerabilities. This was indeed the scenario with the machines that we analyzed.
Responsible Disclosure
We contacted the impacted distributors whilst tackling controllers sequentially, with our first speak to in November 2021 and the final one particular in March 2022. The Industrial Management Methods Cyber Crisis Reaction Team (ICS CERT) at Cybersecurity & Infrastructure Protection Company extended a must have aid in the course of the discussion which we are grateful for.
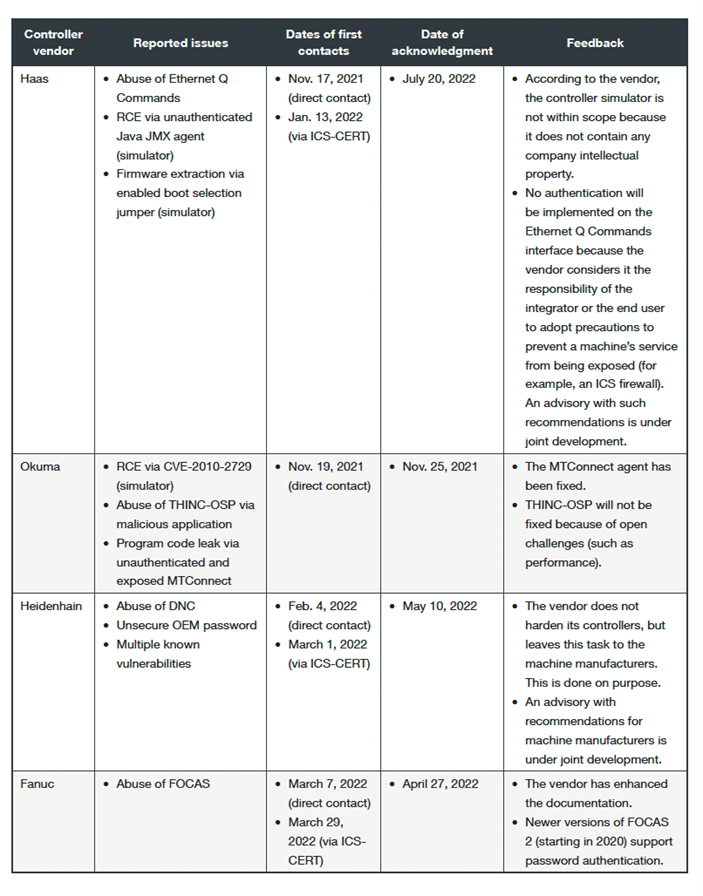
As of this composing, all 4 suppliers have replied to our problems and most of them have addressed, to different degrees, our conclusions in a affordable time body. Extra importantly, all of them have expressed interest in our investigation and have determined to enhance possibly their documentation or their conversation attempts with their equipment makers, with the last work of supplying conclude consumers far more protected answers.
To master extra about the safety dangers confronted by CNC equipment, download our complete report here.
Tags
sXpIBdPeKzI9Laptop2p0SWMpUSM2NSxWzPyXTMLlbXmYa0R20xk